SSL Virus
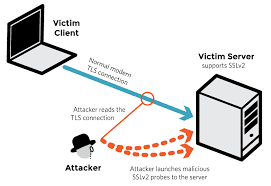
SSL is a method of encryption used by various network communication
protocols. Conceptually, SSL runs above TCP/IP, providing security to users
communicating over other protocols by encrypting communications and
authenticating communicating parties. SSL DDoS attacks and SSL DoS attacks
target the SSL handshake mechanism, send garbage data to the SSL server, or
abuse functions related to the SSL encryption key negotiation process. SSL
attacks in the form of a DoS attack can also be launched over SSL-encrypted
traffic, making it extremely difficult to identify.
A single standard home PC can take down an entire SSL-encrypted web
application, and several computers can take down a complete farm of large,
secured online services. SSL attacks are popular
because each SSL session handshake consumes 15 times more resources from the
server side than from the client side. Such attacks are "asymmetric"
because it takes significantly more server resources to deal with the attack
than it does to launch it.
Encrypted-based HTTP (HTTPS Flood)
Attacks
Many online businesses increasingly use SSL/TLS (Transport Layer
Security) as part of web application security to encrypt traffic and secure end-to-end
data transit. DoS attacks on encrypted traffic are on the rise. HTTPS floods -
floods of encrypted HTTP traffic - are now frequently being used in
multi-vulnerability DDoS attack campaigns. Compounding the impact of
"normal" HTTP floods, encrypted HTTP attacks add several other
challenges, such as the burden of encryption and decryption mechanisms,
complicating DDoS attack prevention efforts.
THC-SSL-DoS Attacks
The Hacker's Choice (THC), an international group of security
researchers and hackers, developed this proof of concept tool to encourage
vendors to patch SSL vulnerabilities and offer anti-DDoS protection.
THC-SSL-DoS require only a small number of packets to cause denial of service
(DoS) for a large server. It initiates a regular SSL handshake, then
immediately requests renegotiation of the encryption key. The tool repeats this
renegotiation request until all server resources have been exhausted.
Protecting Against SSL Attacks
Most DDoS mitigation services do not actually inspect SSL traffic, as
doing so would require decrypting the encrypted traffic. Moreover, mitigation
of SSL attacks requires extensive server resources. Countering SSL DDoS attacks
thus poses several challenges, including the burden of implementing encryption
and decryption mechanisms. As a result, these serious attacks require extremely
sophisticated DDoS mitigation and DDoS protection solutions.




Comments
Post a Comment